Be Prepared To Fight Cybercrime With User Training
In the tech industry today, even the most reliable tools can be used against you. Five Nines has recently discovered phishing attempts that are in...
Five Nines Team : Dec 15, 2025 10:00:00 AM
1 min read
Small and midsize businesses are prime targets for increasingly frequent, damaging cyber-attacks, so security can’t be an afterthought.
There is no single tool that stops every threat; real protection comes from layering the right technologies and practices across your environment.
Your people are ultimately the strongest (or weakest) line of defense, so proactive training and open conversations about risk are just as important as technical tools.
Small to medium-sized businesses are consistently targets of cyber-attacks due to their size and underestimated security measures. According to the ITRC 2025 had a record total of 3,332 data compromises last year, a 79% increase in just five years.
It's time to prioritize your IT environment, and it's time to sleep soundly at night knowing your business has what it needs to stay protected.
Protecting your business from a cyber-attack is about investing in and utilizing the right tools for the right protection. Covering all of your bases in terms of security is the only way to confidently fight cyber-attacks, and these aspects can range from monitored firewalls or intrusion prevention systems to managed vulnerability scanning of networks, servers, and databases. According to the report above, the root causes of these significant data breaches range from system errors to employee negligence. There is no "one tool fights all" solution, but the combination of the right tools will make your IT environment that much stronger.
You've heard rumors about the cost of securing your IT environment, but what you don't hear about is the money that could be lost due to a cyber-attack. According to Cybercrime Magazine ransomware costs are estimated to reach $74 billion in 2026, making it the greatest threat to companies around the world.
It's important to stay ahead of the curve, as the risk of a cyber-attack consistently increases.
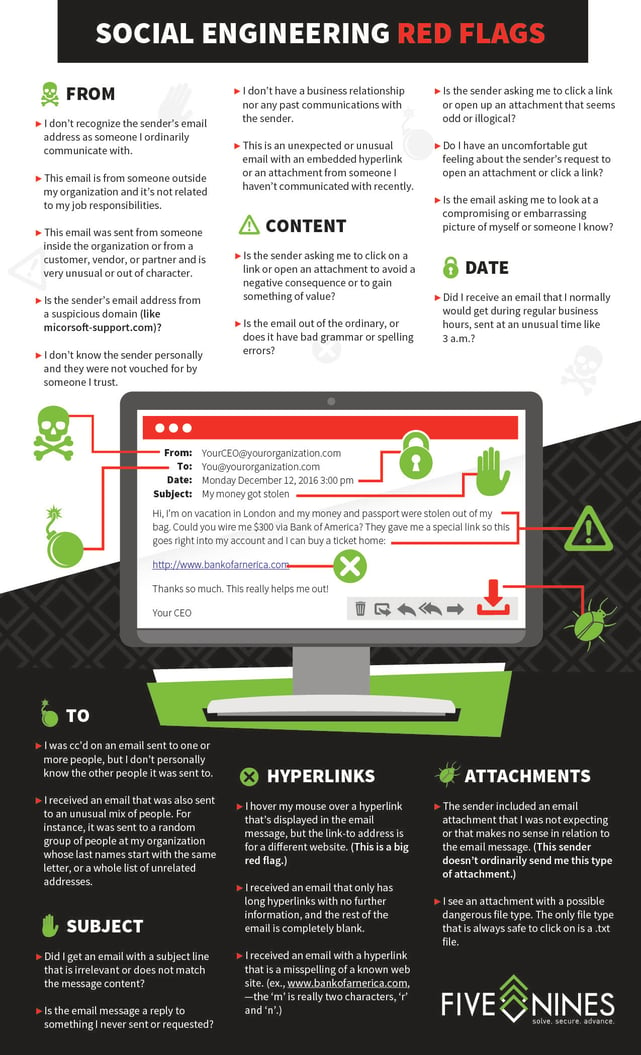
Prevention starts with a conversation. Recognizing that you don’t know what you don’t know, and giving yourself permission to ask for help. Fighting the cyber-era is about being proactive, and implementing the right team and tools for a safe and successful IT environment. Regardless of the amount of time or money you spend on implementing tools to safeguard your environment, the first, last, and BEST line of defense is your people. There is no substitute for the human element. If you’re not leveraging the collective asset of your people, then it’s only a matter of time before a compromise occurs.
Cyber-attacks are becoming more targeted and severe as technology advances, but they also provide a real opportunity for businesses to focus on true IT security methods. Avoid vulnerability and make it a priority to add value to your technical environment.
There is a Five Nines Difference. To learn more about the service model that sets us apart, contact us today!
Because attackers assume smaller organizations have fewer defenses, less dedicated security staff, and more gaps in their systems and processes. That combination makes it easier to exploit both technical weaknesses and human mistakes.
It means using a layered approach: monitored firewalls, intrusion prevention, endpoint protection, vulnerability scanning, patching, backups, and more. No single product can block every attack, so multiple controls work together to reduce risk and limit damage.
Yes. While security tools and services require budget, the financial and operational impact of a successful attack — downtime, data loss, reputation damage, potential fines, and ransom demands — can be far greater than the cost of prevention.
Start with a conversation and an honest assessment. Identify your most critical systems and data, review current protections, and look for obvious gaps in areas like patching, backups, access control, and employee awareness. From there, you can prioritize improvements.
Because many attacks depend on someone clicking a link, opening an attachment, reusing a weak password, or ignoring warning signs. When employees are trained to recognize suspicious activity and follow good security habits, they can stop threats before technology even gets involved.

In the tech industry today, even the most reliable tools can be used against you. Five Nines has recently discovered phishing attempts that are in...

The AT&T phone record breach – which took place in 2022 and was disclosed July 2024 – affects everyone. Even if you're not an AT&T customer,...

Wi-Fi. It's a symbol that everyone recognizes, a term that most people are familiar with, yet many business' Wi-Fi networks are left unprotected and...